Defending Against Matt Blaze
Matt Blaze has published a paper, Rights Amplification in Master-Keyed Mechanical Locks. Here he describes how anybody given a key only to their own office can use it to create a master key that operates every lock in the building. This technique has been heavily promoted in the burglary community and is available for download from every burglary forum.
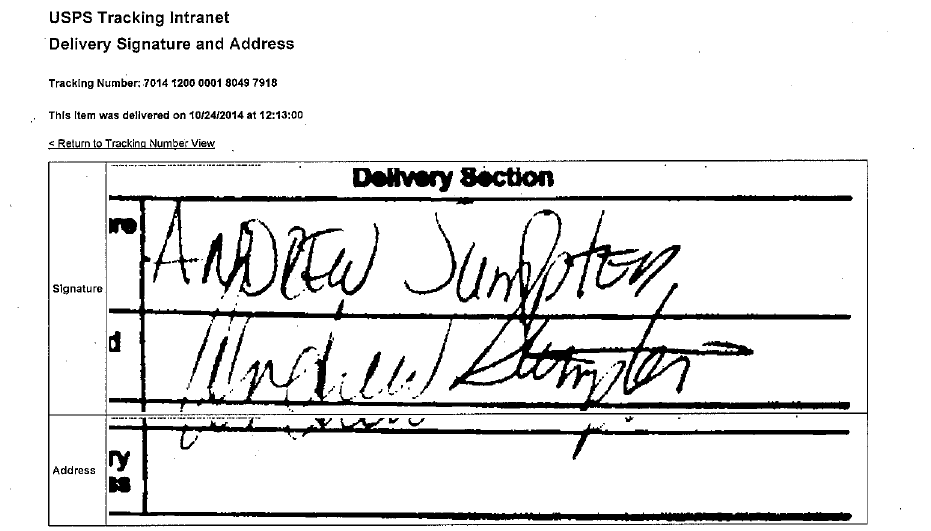
See my PDF file, Mail-Order Cores that Defeat Matt Blaze, to see what I am doing about this threat. The image below is of a certified mail receipt recording when I sent Mr. Blaze some cores to test his skills on. I wait for a reply.
Matt Blaze’s original paper was a bit opaque due to his use of terminology from cryptography, a field that the typically illiterate burglar is unfamiliar with. But the burglary forums have many threads started by the more literate members to interpret Mr. Blaze’s paper for the less literate members, so I am not giving anything away when I summarize the technique here.
First I will describe standard practice among locksmiths and then I will describe practices that exist but are considered advanced. My mail-order cores are way beyond advanced, but I am not going to describe how they work; the fact that Mr. Blaze is stumped is proof enough that they do work.
Standard Practice
The depths of the cuts on a key come in discrete increments and this is set by the manufacturer. For instance, Kwikset has six possible depths (numbered 1 to 6) in increments of 0.023” and Schlage has ten possible depths (numbered 0 to 9) in increments of 0.015”. 0.023” is the thinnest master pin available; any thinner and it would get stuck between the plug and the cylinder. Also, keys that differ by 0.023” will not interchange unless the locks are much worn, but keys that differ by only 0.015” might interchange with a little jiggling.
It is standard practice to masterkey Kwikset in single steps. For instance, if the master key is 1 4 3 5 2, an apartment key (Kwikset is used on apartments but almost never on commercial buildings) might be 2 3 2 4 3. This is called a single-step masterkey system.
It is standard practice to make each pin chamber of a Schlage system either even or odd. For instance, if the master key is 7 4 3 1 0, then only even numbered cuts will be used in the second and fifth spaces while only odd numbered cuts will be used in the first, third and fourth spaces. This assures that no master pins thinner than 0.030” are ever needed and that no two office keys will ever differ from each other by less than 0.030”. For instance, 3 6 5 5 2 is acceptable but 4 7 4 4 1 is not because it requires 0.015” master pins in the third and fifth chambers and also because it differs from 3 6 5 5 2 by only 0.015” and might jiggle that lock open. This is called a double-step masterkey system.
If all of the pin chambers have a master pin in them, the system is called total position pinning (TPP) and is common to the point that probably nineteen out of twenty locksmiths have never done anything else. I own my own company now and write my own software to generate masterkey systems, but every locksmith that I have ever worked for in my thirty-year career used HPC Masterking software, which always generates TPP systems and always sets the first change key to be exactly one depth deeper than the master key in single progression systems and exactly two depths deeper in double progression systems. Then they increment the change keys like the odometer on a car. How predictable!
For instance, suppose the locksmith is asked to generate a small Schlage system with only four change keys and he specifies a master key of 7 4 3 1 0. This is what he gets:
| 7 4 3 1 0 | master |
| 9 6 5 3 2 | key #1 |
| 9 6 5 3 4 | key #2 |
| 9 6 5 3 6 | key #3 |
| 9 6 5 3 8 | key #4 |
If a fifth change key is needed, it will be 9 6 5 5 2 because the list of change keys is being incremented like the odometer on a car. Honestly, this is really stupid. Incrementing the change keys like an odometer was obviously done by someone who thought that the FOR/NEXT loop in the BASIC programming language was the most advanced computer programming technique ever conceived. My masterkey systems are definitely NOT incremented like an odometer. My mail-order cores are delivered to the customer in pseudo-random order; receiving one core does not predict any of the cuts on the key to the next core.
Note that all of the locks have four #2 master pins that serve no purpose. They make the locks easier to pick by introducing more shear lines and yet they do nothing to distinguish one change key from another. HPC Masterking is notorious for producing really easy-to-pick locks, yet they have never corrected this flaw. Also, the locksmith spends a lot of time inserting #2 master pins in the locks, which wastes his time and sometimes results in his running out of pins and having to drive across town to the locksmith supply shop to buy a few more vials of #2 pins.
The Blaze Attack against Standard Practice
Suppose that your office key is 9 6 5 3 6; that is, you are in office #3 of the system shown above.
You will progression one space at a time to see what other cuts operate the lock.
First progression:
| 1 6 5 3 6 | No. |
| 3 6 5 3 6 | No. |
| 5 6 5 3 6 | No. |
| 7 6 5 3 6 | Yes. |
So the first cut of the master key is a 7.
Second progression:
| 7 0 5 3 6 | No. |
| 7 2 5 3 6 | No. |
| 7 4 5 3 6 | Yes. |
| 7 8 5 3 6 | No. |
So the second cut of the master key is a 4.
We continue in this way by progressing the third, fourth and fifth spaces to determine that the master key is cut to a 3, 1 and 0 depth, respectively. Thus, in five progressions, the attacker has figured out what the master key is: 7 4 3 1 0
Clearly, HPC Masterking is particularly weak against a Blaze attack. If two employees conspire to figure out what the master key is, comparison of their keys makes it obvious that they only have to progression the fifth space.
| 9 6 5 3 0 | Yes. |
| 9 6 5 3 2 | No. |
| 9 6 5 3 4 | No. |
| 9 6 5 3 8 | No. |
So the fifth cut of the master key is a 0. In fact, against HPC Masterking, the very first key the attackers cut, 9 6 5 3 0, functions as a master key and they need make no further experiments.
Rotating Constant
When I first took up the study of locksmithing I was sixteen years old and taking the [in]famous Foley Belsaw course. They taught TPP as not just standard but the only way to masterkey locks. It occurred to me that the locks would be more difficult to pick without the superfluous #2 master pins. We could masterkey only the last two pin chambers like this:
| 7 4 3 1 0 | master |
| 7 4 3 3 2 | key #1 |
| 7 4 3 3 4 | key #2 |
| 7 4 3 3 6 | key #3 |
| 7 4 3 3 8 | key #4 |
| 7 4 3 5 2 | key #5 |
| 7 4 3 5 4 | key #6 |
| 7 4 3 5 6 | key #7 |
| 7 4 3 5 8 | key #8 |
| 7 4 3 7 2 | key #9 |
| 7 4 3 7 4 | key #10 |
| 7 4 3 7 6 | key #11 |
| 7 4 3 7 8 | key #12 |
| 7 4 3 9 2 | key #13 |
| 7 4 3 9 4 | key #14 |
| 7 4 3 9 6 | key #15 |
| 7 4 3 9 8 | key #16 |
If we needed more than sixteen change keys, we could masterkey two other pin chambers like this:
| 7 4 3 1 0 | master |
| 7 6 5 1 0 | key #17 |
| 7 6 7 1 0 | key #18 |
| ... | |
| 7 2 1 1 0 | key #32 |
Then – and this is the clever part – it occurred to me that the two chambers masterkeyed did not have to be completely different. They only had to differ in one position. Above, I demonstrated masterkeying spaces four and five; then I demonstrated masterkeying spaces two and three. But there are actually ten such combinations:
| Spaces 1, 2 |
| Spaces 1, 3 |
| Spaces 1, 4 |
| Spaces 1, 5 |
| Spaces 2, 3 |
| Spaces 2, 4 |
| Spaces 2, 5 |
| Spaces 3, 4 |
| Spaces 3, 5 |
| Spaces 4, 5 |
In the system described above, there are 10×42=160 possible change keys, minus a few that violate the maximum adjacent cut specification (MACS) because keys cannot be cut with a steep ramp from very shallow to very deep cuts. This is about a sixth of the 45=1024 possible change keys provided by the TPP method, again minus a few that violate the MACS. But the great majority of masterkey jobs are for small facilities with only a dozen or so locks, so 160 is plenty. Reducing the number of possible change keys does not generally outweigh the advantage that the locks are easier to pin with only two master pins per lock and that they are more resistant to picking. 5C3 is also 10 (verify) and so having three master pins would provide 10×43=640 possible change keys.
Much to my dismay, I would later learn that this is not an original invention. It is called the rotating constant (RC) method of masterkeying and, while almost unknown to private locksmiths, it is used by manufacturers when they supply factory masterkeyed locks to contractors. Kwikset, in particular, makes most of their money selling to the builders of apartments and they use the rotating constant method with four chambers having master pins and one without. (The system described above has two chambers with master pins and three without.) Note.
The Blaze Attack against Rotating Constant
There are a few locksmiths around who have heard of the rotating constant method and, exalting in their “advanced” status, have made outrageous claims about its effectiveness. When Matt Blaze’s paper came to their attention, some of these self-described experts immediately claimed that their highly advanced techniques thwart him. In fact, the rotating constant method is no obstacle to a Blaze attack.
Suppose that your office key is 7 4 3 3 8; that is, you are in office #4 of the system shown above.
You will progression one space at a time to see what other cuts operate the lock.
First progression:
| 1 4 3 3 8 | No. |
| 3 4 3 3 8 | No. |
| 5 4 3 3 8 | No. |
| 9 4 3 3 8 | No. |
So the first cut of the master key is a 7. None of the other possible cuts in this space worked, so the master key and the change key must agree in their first cut; that is, the first cut is constant.
For those that are not constant, the Blaze attack is the same as it was for the TPP method. So nothing has changed provided only that the attacker is aware that the change key may sometimes equal the master key in certain spaces. Mr. Blaze (p. 7) was aware of this:
Some of the less literate discussants on the burglary forum (e.g. the one called Evan) who claim to be master thieves, well-versed in divining the master key to any facility where they get a temporary job, have clearly not actually read Matt Blaze’s paper. But the more literate discussants explained it to them, so I am not giving anything away here when I point out that the rotating constant method does not actually stymie a Blaze attack.
FYI A few – actually a very few – of the burglary forum discussants are clever. But most are just brutish illiterates struggling to interpret Matt Blaze’s paper in the same way that head hunters in Borneo might struggle to interpret a Bible that they found among a missionary’s personal effects – after they cooked and ate him.
Split Pins
Burglary forums such as Lockpicking 101 are open to everybody, including felons incarcerated for burglary who are logging on from the computers in the prison library or – where the warden has blocked this URL – from Android phones smuggled into the prison. They openly boast of their incarceration and are given special standing for their “experience” by the moderators!
There are also locksmith forums that carefully vet their discussants, making them prove that they are bonded locksmiths who are running or employed by legitimate businesses. I am a member of some such forums. But the fact that the discussants are legitimate does not imply that they know anything about masterkeying beyond how to download and operate HPC Masterking.
When I started selling my mail-order cores, one locksmith immediately pulled a new method out of his ass and claimed to have always done this and to have always been immune to the Blaze attack. He writes that he uses the TPP method as prescribed by HPC Masterking software (the only method/software that he is familiar with) but, whenever it calls for a #8 master pin, he uses two #4 master pins.
For instance, suppose our guru is asked to generate a small Schlage system with only four change keys and he specifies a master key of 7 4 3 1 0. This is what he gets:
| 7 4 3 1 0 | master |
| 9 6 5 3 2 | key #1 |
| 9 6 5 3 4 | key #2 |
| 9 6 5 3 6 | key #3 |
| 9 6 5 3 8 | key #4 |
But, cleverly, when he keys up the fourth lock, he uses two #4 master pins in the fifth chamber.
Just by chance, let us assume that it is the guy in the fourth office who attempts a Blaze attack on his employer. The attack works the same against the first four pin chambers and determines that the master key is 7 4 3 1 –. But, when the attacker gets to the fifth pin chamber, this is what happens:
| 9 6 5 3 0 | Yes! |
| 9 6 5 3 2 | No. |
| 9 6 5 3 4 | Yes! |
| 9 6 5 3 6 | No. |
Is this totally confusing or what? The master key is either 7 4 3 1 0 or 7 4 3 1 4. Stumped? Not exactly. When the attacker makes his daring approach to the cash office, he will simply have to bring two potential master keys: 7 4 3 1 0 and 7 4 3 1 4. Trying them both will take an extra ten seconds beyond the standard Blaze attack.
What if the guy in office #4 is not the thief, but one of the other three? The modification to the lock on office #4 does nothing – not even add ten seconds – to stop the other three from using the standard Blaze attack to gain entrance to the cash office.
But what about the guy in office #2? 9 6 5 3 4 works in office #4. Isn’t that amazing? While adding an extra ten seconds to the attack on the cash office by the guy in office #4, our guru has inadvertently given the guy in office #2 access to office #4. Oops!
In sharp contrast, I can provide over six thousand of my mail-order cores and guarantee that nobody’s office key will open anybody else’s office. If you find one that does, then you get your money back on the entire system! Also, I can create a system in which some or all of the change keys operate a common core. For instance, a school may want all the teachers' keys to open the hallway door, or an office complex may want every tenant's key to open the gate in the wrought iron fence. Having a common core reduces the number of possible change keys to less than 1000.
Testing your Current System
Anybody with a chainsaw sharpening file can use the Blaze Attack to create a master key to his apartment complex if it uses Kwikset locks. SFIC cores have much closer tolerances (they increment by 0.0125" instead of 0.023") and – while there are thieves on the burglary forum who boast of having compromised a SFIC system using hand tools – it generally requires a key machine.
A Blue Punch Key Machine costs about $1000, which is too much for the low-level criminals who frequent the burglary forum to buy. But all they would do if they got into your building at night is steal the copy machine. If your business is targeted by other companies attempting to steal industrial secrets, then $1000 is not a lot to spend on the project. And, once they have obtained a master key to your building, they can always sell their Blue Punch on eBay to recoup that cost.
If you wish to test your current SFIC system to see if it is really as insecure as I describe in this blog, just mail me a copy of your office key and $100. I will mail you 28 SFIC keys for you to try in your office lock. Test them all and tell me which ones work. Then I will mail you a master key to your building. If you agree to purchase my cores to replace your system, I will deduct the $100 from the cost of the cores.
Comparison with HPC Masterking
An Anti-Blaze Masterkey system is divided into low-, medium- and high-level cores. The low- and medium-level cores have only six pins so, when an attacker has found what he thinks to be the master key, he still has to approach the high-level core ten times to try it with a 0, 1,…, 9 cut in the seventh position. But the Blaze Attack does not work on the six-pin cores, so what the attacker thinks to be the master key almost never is and he winds up approaching the high-level core hundreds of times.
Most locksmiths have used HPC Masterking their entire career and thus assume that it is the only software available. Claiming to have written my own software is met with the same incredulity as if I had told them that – dissatisfied with Toyota – I had built my own car. Thus, since tweaking HPC Masterking is as far as their own imaginations extend, it is generally assumed that all I actually did was set the number of pin chambers at six when running HPC Masterking and then I manually added a seventh pin to the high-security cores.
Naturally, being the self-proclaimed gurus that they are, within minutes of hearing about my Ant-Blaze Masterkey System and learning of the mysteriously empty pin chamber in the low- and medium-level cores, the locksmith forums were suddenly alight with discussants claiming to have always left one pin chamber empty and to have always been immune to a Blaze attack.
Let us see how the two systems compare:
| Feature | HPC Masterking, Six Pins | Anti-Blaze Masterkey System |
| Total available change keys | Over 6000.5700 is guaranteed for initial orders of 100, 4600 for initial orders of 30 and 3600 for smaller initial orders. | |
| Any two change keys differ from each other by at least 0.025” in at least one position | Yes. | Yes. |
| Autocorrelation: A change key provides information about the next one delivered from the locksmith. If he walks down the hallway installing them, that is your neighbor. | Yes. They increment like an odometer. Since the list of 4000 keys is 400 pages long, locksmiths cannot manually randomize it. | No. |
| Pick Resistance | No. | Yes. Medium-level cores have a hook of seven depth increments. The next section explains what a hook is. |
| Blaze attack produces a master key for all six-pin cores | Yes. | No. When carried out on a low-level core, what Matt Blaze says is the master key works on none of the medium-level cores and on only a small fraction of the other low-level cores. |
| Number of approaches to the high-level core needed | Ten. | Hundreds. |
| A control key for one core pulls all the six-pin cores | Yes. | No. None of the others. |
Pick Resistance
All low-, medium- and high-level cores have at least three spool pins, which make them significantly more difficult to pick than SFIC cores without any spool pins. These are special pins that are shaped like a spool of thread and allow the plug to turn slightly as though that pin chamber is at its shear line when, in fact, the pin is still blocking the plug from turning. The presence of spool pins alone is sufficient to stop me and every locksmith I have ever worked alongside from picking the core, but I go even further with my Anti-Blaze Masterkey systems by providing a “hook,” which I will define below.
When picking a masterkeyed lock, it almost always opens to the deepest shear line. Locksmiths can verify this by masterkeying an easy-to-pick cylinder like Kwikset with different colors of bottom and master pins. Then repeatedly pick it, pull the plug out and observe that the master pins are all in the plug. The more energetic methods, like the use of an electric pick gun, may have the pins bouncing around so much that they do not always open at the deepest shear line. But SFIC cores are machined to such tight tolerances that they can only be picked by carefully lifting one pin at a time and, in this case, it almost always catches on the first shear line encountered. Nobody is using pick guns against SFIC.
Picking is made more difficult by the presence of what I call a hook; that is, a long bottom pin with a short bottom pin immediately behind it. For instance, if the pin at the back of the lock (SFIC counts from the tip, so the 1st pin) is a #0 and the pin immediately in front of it (on SFIC, the 2nd) is a #9, it is very difficult to reach behind the #9 pin with a hook pick and lift the #0 pin all the way up to its shear line. Also, if bumping the lock open, it takes a granny bump to lift the #9 pin up to its shear line but a Babe Ruth bump to lift the #0 pin up to its shear line. One cannot be granny and Babe Ruth at the same time. On a masterkeyed core, #0 cannot be the deepest shear line, but #2 can be, so the largest available hook is seven depth increments.
All medium-level cores have a hook of seven. The number of available medium-level change keys is guaranteed to be at least 20% of the total available. I understand that big companies are more top heavy in management so, for those who purchase large systems, I can deliver over 37% as medium level if they need that many. For instance, a grocery chain may require three keys per store; the manager’s office (medium level), the assistant manager’s office and the exterior. I can provide them with 1840 sets of keys and still have over 400 medium-level change keys available for the warehouse and front office.
On systems of all sizes, the high-level cores are guaranteed to have a hook of seven or more depth increments and, furthermore, there is no master pin in either chamber, so you do not have to believe my claim that cores are usually picked to the deepest shear line since there is only one shear line. If the lock picker lifts the long bottom pin up even slightly while groping for the short bottom pin behind it, then the long bottom pin is past its only shear line. On systems of all sizes, there are 72 available high-level change keys and they are all guaranteed to never inadvertently operate as a sub-master for any of the low- or medium-level cores.
Note that, in the paragraphs above, we are assuming that the management is fearful of either lock pickers or of a Blaze attack on their medium-level office doors. This is reasonable since their employees include both programmers who are capable of reading Matt Blaze’s paper and also technicians whose work requires steady hands and are thus capable of learning to pick locks. However, the situation in a high-rise luxury apartment is different. The rich people who live there probably cannot pick locks, but they are consumed with envy for the even richer people in the upper floors and thus might buy a Blue Punch and carry out a Blaze attack against them. At the same time, the exterior doors have easy avenues of escape and thus it is feasible for a professional burglar to spend hours working on picking open an exterior door. But once inside he is not going to be picking locks; he will enter apartments through subterfuge and/or at gun point.
The solution is to make the exterior doors low level against a Blaze attack but to reserve for them the change keys that have a hook of seven depth increments. Inside, the lower floors are low level, the upper floors are medium level and the penthouse is high level. Like all high-level cores, the penthouse cores have a hook of seven or more depth increments and there is no master pin in either chamber. But the apartments below them get cores with no regard for how much of a hook they have. I can provide a system like this for a high-rise apartment with over 6000 units.
It is possible to put common cores on the exterior doors of a high-rise apartment; that is, cores that can be opened by every tenant’s key to save them the burden of carrying two keys. However, this reduces the available change keys to less than a thousand and it reduces the pick resistance of the exterior doors. This is not a feature that can be offered to all the tenants of a large high-rise and, even for smaller buildings that require fewer than a thousand change keys, it is not recommended for security reasons. It is really meant for compounds with a wrought iron fence that is there mostly for decoration and to prevent pedestrians from cutting the corner of the intersection by walking through the compound.
I aim to please. Since these cores are sold by mail order, you do not have to tell me the name or location of your business; I am fine with being paid by money order and with shipping to a Post Office box. But it does help if you can tell me whether you are securing a chain of retail stores, a high-rise luxury apartment building, a fortress-like factory where every worker has a key to his personal workspace, or what. Having written this software myself, I can tailor it to your particular security needs in a way that the typical HPC Masterking monkey could never do.